What is Rdntocdns.com?
Rdntocdns.com is a malicious website that redirects users' web browsers, namely Google Chrome and Microsoft Edge. There are two primary reasons why this domain redirected the browser: it is either the user visited a malware-infected website or adware is currently installed on the computer.
The aforementioned domain sends malware-infected internet browsers to undesired websites, such as bogus virus alerts, illegal gambling platforms, and adult video chat sites, which can be inconvenient for visitors seeking a secure surfing experience.
Malicious domains in general
Rdntocdns.com is an insecure domain since its root URL does not lead to a website and is used for malicious activities. This can involve redirecting the web browser to malicious websites, drive-by downloads, or any other sites that the cyber criminals who run the rogue domain want the infected browser to view. It can also be used to display phishing websites; although not technically accessible from the root domain, it may contain malicious URLs that load when executed.
Malicious domains can also serve as a command and control server (C2), which is the hostname or URL that hackers use to run an infected system. They can use the malicious domain name to send commands and carry out tasks on malware-infected systems.
However, these are the more serious types of harmful domains; some of the most prevalent domains in these categories are largely used to redirect clients and display malicious advertisements by tricking users into granting permission to display ads via web browser notifications.
Rdntocdns.com threat behavior
After additional investigation of Rdntocdns.com, we discovered that it redirects us to an unknown URL whenever we visit a malware-infected website, notably those that use the WordPress CMS. The aforementioned domain is part of the Balada injector, a well-known WordPress malware, and Rdntocdns.com is one of the malware's new redirect domains, which it uses to redirect compromised WordPress sites and unsuspecting visitors to malicious URLs.
Aside from that, it can reroute the browser if it is infested with adware. Although not intrinsically dangerous, this form of malware infection can cause serious damage to the computer and browser.
These redirects are typical while accessing fraudulent websites, such as illegal torrenting platforms and pirated download sites. Despite the fact that we had not previously visited any of these types of websites, Rdntocdns.com pointed us to the page when we launched the browser.
We also noticed that it automatically launches the browser to redirect to Rdntocdns.com, even if it is not already open. We did not click any malicious ad elements, but they are still there, which is dangerous since they can divert the browser; who knows if the next time it redirects the browser unexpectedly, malicious software will be placed on the computer?
How Rdntocdns.com infects a browser
When a user visits a malware-infected WordPress website, Rdntocdns.com can reroute their browser. Because a large number of websites online use the aforementioned CMS to host and manage content, fraudsters may discover several gaps and vulnerabilities to exploit these sites, which receive hundreds of thousands of visitors.
Advertising-supported software, commonly known as adware, can be placed on a computer through a variety of means and could be the source of Rdntocdns.com. This includes malware-contaminated torrent files and executables. However, in most situations, it is packaged alongside third-party installers accessible in a variety of program and application marketplaces; so, we urge that you always read the installer carefully to avoid mistakenly downloading bundled applications.
Summary of the threat
| Malware name | Rdntocdns.com |
| Threat type | Redirect, Adware, Malicious domain |
| IP address | 45.9.149.210 |
| Delivery network | Third-party installers, malicious payloads |
| Malware behavior | Redirect the browser to unwanted websites |
| Damage | Potential malware infection |
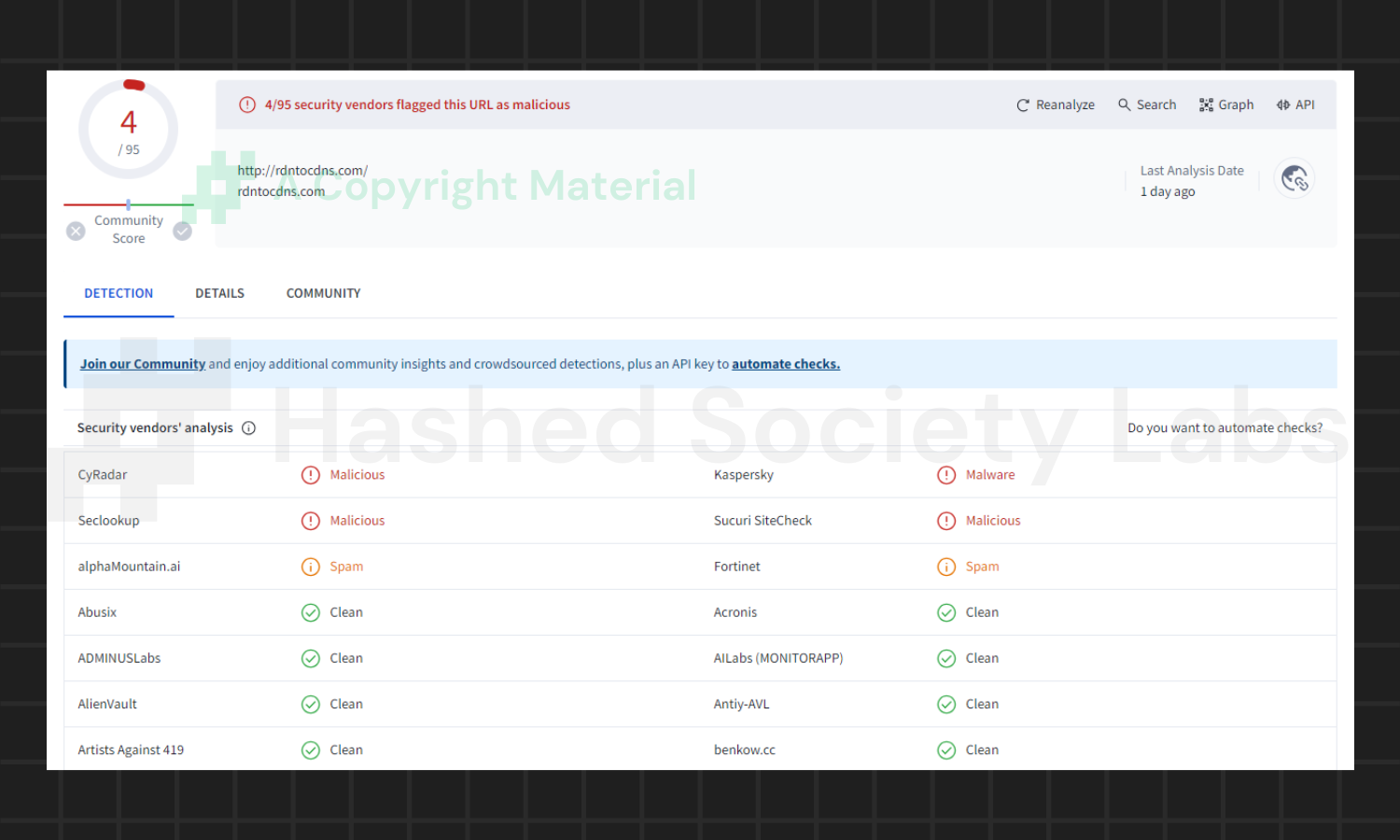
| VirusTotal detections | 4/95 antivirus flagged this domain (See results) |
More about Rdntocdns.com
If you keep visiting the same site or if adware remains installed on your machine, Rdntocdns.com will most likely continue to reroute your web browser. It will reroute the browser to unfamiliar websites without the user's permission, so we believe this type of threat is hazardous and should be deleted to limit the risk of the user being directed to a dangerous drive-by malware download.
To stop Rdntocdns.com from opening your web browser and redirecting you to unknown websites, please follow the official step-by-step instructions below.
You are in luck if you need help getting rid of Rdntocdns.com from your computer. The following malware removal instructions will show you how to do just that. Make sure to carefully follow the steps to make sure the threat is completely gone. We considered the technical skills of the people who use the internet, so we made sure the steps are simple enough that even those who aren't tech-savvy could follow them. Before you continue, make sure you have a backup of your data. If you don't, your files may be destroyed or lost while completing the instructions below. These kind of situations are uncommon, but we recommend doing so just in case. Remove Rdntocdns.com Instantly Poor protection often leads to malware infection. Let Bitdefender, the world’s leading antivirus, handle Rdntocdns.com with ease. It's time to stop worrying about malware. We've teamed up with Bitdefender to offer Hackerdose visitors an exclusive 50% discount on their products. Now is the time to start taking your computer security seriously with the best antivirus on the planet. To remove Rdntocdns.com from your browser, you only need to follow a simple three-step procedure: Step 1: Delete malicious extensions Step 3: Uninstall unwanted software Extensions can be the leading cause of Rdntocdns.com causing issues with the browser. However, it may be difficult to remove them if certain browser policies are set to make it persist. It might disable the delete button which makes it hard to do so. For this reason, we will first need to delete the policies it has set on the browser before attempting to remove unwanted extensions. How to remove Google Chrome browser policies: 1. To do this, we will use Chrome Policy Remover. Download the Windows version by clicking here. 2. Proceed to download delete_chrome_policies.bat by clicking Download anyway. 3. Once the bat file has finished downloading, run it as administrator to begin removing unwanted policies set by the malware. 4. If the Microsoft Defender SmartScreen prevented it from running, click Run anyway. This tool has been recommended enough times in the Google Chrome community therefore we can vouch that it is safe to run. (VirusTotal results of the Policy Remover.) 5. The command prompt will open up, it will close Chrome and delete certain malicious policies. Once the policies are removed, you can now close the command prompt and begin removing the extension. How to delete unwanted extensions from Chrome: 1. Open Google Chrome and click the three horizontal dots on the upper-right corner of the screen. 2. From the dropdown menu, select Extensions and click Manage Extensions. 3. You should now be able to click the Remove button. Continue to do so in order to remove the unwanted extension from the browser. (For this example, we will be using Google Docs Offline.) How to remove Mozilla Firefox browser policies: 1. Open the browser and type about:policies in the address bar. 2. Take note of the active policy names as shown on the screen. 3. Press Windows Key + R to open the Run command. 4. Type regedit and hit enter to open the Registry Editor. 5. Go to the following directory: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Mozilla\Firefox 6. Delete the policies that matched the ones shown on the browser policy page earlier. With this, we can proceed with deleting the unwanted extension. How to remove unwanted extensions from Firefox: 1. Open the Firefox browser and click the extension icon on the upper-right corner of the screen. 2. Click on the cog icon near the unwanted extension you want to install. From the dropdown menu, select Remove Extension. (We will be using a sample extension to demonstrate.) How to delete browser policies set in Microsoft Edge: 1. Open Command Prompt as administrator. 2. Type in the following code and enter each line separately. 3. Once finished, close Command Prompt and we can begin removing the unwanted extension/s from the browser. How to remove unwanted extensions from Microsoft Edge: 1. Open Microsoft Edge and click the Extensions icon on the top bar of the browser. 2. Click on Manage Extensions. 3. Find the unwanted extension and click Remove. AdwCleaner is a utility tool that is primarily used for cleaning adware and potentially unwanted applications (PUP) from the computer. This program is also primarily used to find and remove malware that is targeted at the web browser. Here's how to install and use AdwCleaner: 1. To start, download the latest version of AdwCleaner. 2. Once AdwCleaner has finished downloading (adwcleaner.exe), run the executable file. 3. If the User Account Control window pops up, click Yes to proceed with running the program. 4. Once the program has launched, agree to the End User License Agreement by clicking the I Agree button. 5. Click on the Scan Now button to begin scanning your computer for browser threats such as adware, PUPs, and more. 6. Wait for AdwCleaner to finish scanning the files on the system. This may take a while depending on how large the files on your device are, as well as your system's hardware capabilities. 7. Once the scan is complete, proceed to take action by following the on-screen instructions. Otherwise, if the scan shows a clean result, click Run Basic Repair to reset Winsock and other settings before finishing the process. Another possible source of the Rdntocdns.com redirect is malicious software. Such malware might be able to change browser settings in order to support the aforementioned browser threat. As a result, you should check your computer for unknown programs that you did not install. While the latest version of Windows allows you to accomplish this through the Add & Remove Programs section, it is still far simpler to use the Programs and Features page in the Control Panel. The publisher name, the installation date, and the version number will all be displayed in a single grid screen, making it simpler to locate the malware. Here's how to do so: 1. Click on the Windows key to open the Start menu. 2. Type Control Panel in the provided search bar and select the first item from the search results. 3. Click on Programs and inside, select Programs and Features. 4. You will be presented with a list of programs currently installed on your computer. 5. Find programs you do not recognize and right-click the item then select Uninstall/Change from the dropdown menu. We'll need to use a powerful uninstaller to do the dirty work for us if the software is stubborn and won't go away with normal approaches. Fortunately, there are tools for this; Revo Uninstaller is a good uninstaller program made to tackle and remove uninstallable programs. 1. To start, download Revo Uninstaller by clicking here. Avoid downloading from third-party sources as they may contain additional bloatware upon installation. 2. On the download page, opt for the free version of Revo Uninstaller as it has all the features we need. Click on Free Download to begin downloading the setup file. 3. The revosetup.exe file would have started downloading. Click on it to start installing the software. 4. Revo Uninstaller setup would now begin and follow the typical setup procedure such as selecting your setup language, accepting the license agreement, and selecting the installation location. Once setup is ready click Install. 5. After the setup is finished, check the Launch Revo Uninstaller option to open the program upon closing the installer. 6. Once Revo Uninstaller has opened, it will show you the list of applications currently installed on the computer. Find the unwanted program/s, right-click it, and select Uninstall from the drop-down menu. (We will be using PC App Store to demonstrate.) 7. A confirmation message stating if you are sure you want to uninstall the said program, click Continue. 8. Follow the uninstallation instructions and this time, Revo Uninstaller would have forced the program to continue with the uninstallation compared to the previous attempt via Control Panel. 9. You will be notified that the software has been uninstalled, Revo Uninstaller will now conduct a preliminary examination and get rid of additional files and registries related to the unwanted program. 10. On the selection of Scanning modes, select Advanced to make sure everything is scanned without leaving a single directory unnoticed. 11. Wait for the scan to finish as Revo Uninstaller is checking for residual files and registries related to the suspicious program. 12. Revo Uninstaller may have found leftover Registry items, click Select All and proceed to delete them by clicking the Delete button next to it. After that, click Next. 13. It may have also found some leftover files and folders, simply do the same by clicking Select All and deleting them. Now click Finish and the uninstallation of the program is done. When it comes to browser-targeted malware, it will alter the browser settings for the threat to persist. Therefore simply changing the search engine back to default may not work in many cases. If malware still persists, we should reset the web browser to its default settings from when it was first installed. This will get rid of all the configurations the browser threat has set. Note: Resetting the browser will get rid of all the data except for saved bookmarks and passwords. 1. Open the Chrome browser and click the three horizontal dots at the upper-right corner of the screen. 2. On the dropdown menu, scroll down to the bottom and click Settings. 3. In the left sidebar, scroll down and find Reset settings. 4. Click on Reset settings to their original defaults. 5. A confirmation window will appear, click Reset settings to proceed. 1. Launch the Firefox browser and click the hamburger menu on the upper-right corner of the screen. 2. From the dropdown menu, scroll down and click on Help. 3. Inside the Firefox help menu, click More troubleshooting information. 4. Under Give Firefox a tune up, select Refresh Firefox… to reset the browser. 5. A confirmation window will appear, proceed by clicking Refresh Firefox. 1. Run Microsoft Edge and click on the three horizontal dots on the upper-right side of the screen. 2. From the dropdown menu, select Settings. 3. Open the hamburger menu, scroll down, and select Reset settings. 4. Inside Reset settings, click on Restore settings to their default values. 5. A confirmation window will appear, click Reset to proceed. After the web browser has finished resetting, download the important extensions you previously used, and pin the tabs you once had. Set it the way it was previously configured before the malware infection. As the saying goes: “The biggest vulnerability is the person behind the screen“ So, here are some tips and what you need to know in order to keep your device safe and malware-free in the long run. Make sure that all of the programs in your computer is up-to-date with the latest version released by the developer. The reason behind this is that these updates frequently tackle bugs and issues that malware actors often exploit. The same goes for your computer's operating system, make sure Windows is up-to-date with the latest software update to prevent malware from exploiting a hidden vulnerability. One of the biggest sources of malware infection in a computer system is third-party installations. This happens when a user downloads a certain program from sources that are not the official download links. Some of the common types of sources where malware is present are torrent files, cracked software, and games. Malware often disguises itself as resumes and quotations and threat actors often send thousands of these infected emails to company employees around the world in order to infiltrate their network. Always check where your emails are coming from as there may be a chance that the project attachment you received via email did not actually come from a co-worker. Avoid visiting websites that contain unfiltered advertisements such as illegal streaming websites, cracked software platforms, and links sent out to you by somebody you do not trust. These sites are often linked to redirect chains that load once you click on an ad element on the page. Following this chain often leads to drive-by malware and phishing pages that an average user may eventually fail to notice.Rdntocdns.com removal guide
Step 1: Delete malicious extensions

















taskkill /im msedge.exe /f
reg delete "HKCU\Software\Policies\Microsoft\Edge" /f
reg delete "HKLM\Software\Policies\Microsoft\Edge" /f



Step 2: Remove browser malware with AdwCleaner







Step 3: Uninstall unwanted software





![]() Uninstall malicious program/s using Revo Uninstaller
Uninstall malicious program/s using Revo Uninstaller












Optional: Reset the browser to default settings















Tips to keep your computer safe
Keep every software installed up to date
Avoid downloading files from unknown sources
Be careful with opening email attachments
Do not visit unreputable websites
