NewTab Wonders – Details
NewTab Wonders is a malicious browser plugin that sends every query the users make to Myhoroscopepro.com and a different search engine. It is an extension that acts as a conduit for advertising an undesired search engine by replacing the user's default new tab appearance and search engine, such as Google with Bing or Yahoo.

Your computer is infected if you search in the URL bar and are sent to an undesirable search engine rather than your default one such as Google. It is also linked to the Myhoroscopepro.com redirect, which is a similar browser threat that was most likely produced by the same malware programmer due to the threat's nature of functioning side-by-side.
Malicious browser extensions in general
Malicious browser extensions are a sort of malware that can interfere with the browser. Some of them possess malware characteristics that enable them to record the user's surfing activity, keep tabs on what the user is typing (which is essentially a keylogger), get access to their camera and microphone whenever the user enters the web browser, and, last but not least, modify browser configurations such as the search engine and home tab appearance for the benefit of the malware author.
NewTab Wonders is a malicious program that falls into the last category, changing the appearance of the browser's tabs and the default search engine. Not to add the persistent browser policies it enforces, making it difficult for most users to uninstall. If the uninstall option is disabled, many individuals will have difficulty removing the particular extension.
Malware extensions frequently allow the browser to be “managed by an organization“, allowing the creator to set policies that keep the infection operational. While browser extensions are intended to make our browsing experience easier, hackers always find ways to exploit them and achieve the opposite.
NewTab Wonders threat behavior
NewTab Wonders functions by setting a new home tab appearance to the browser so that whenever the browser or a new tab is opened, users will get to type on the search bar provided by NewTab Wonders which then will lead to the redirection to Myhoroscopepro.com and to either Bing or Yahoo depending on the region you are in.
NewTab Wonders redirect in action:

In comparison to other ways malware authors generate money, the developers of NewTab Wonders earn revenue by redirecting the user to Bing/Yahoo and earning from the points infected people acquire while forced to search. NewTab Wonders operates differently, profiting directly from ads based on the queries it displays.
For those who don't know, Bing and Yahoo provide incentives to users who search on their platforms. These points are earned based on the number of searches you conduct each day as well as the completion of activities. The creator of NewTab Wonders designed it so that it pushes the two search engines onto the user's PCs so that they can search on the platform, but instead of receiving points, the malware authors do.
While NewTab Wonders and its redirection URL Myhoroscopepro.com may not pose a significant threat to user data and are solely focused on getting users to click on their search result links, we have seen that they came from malicious payloads, and the malware that they carried may eventually drop more dangerous malware, so it is best to remove this threat as well as any other malware on your computer.

We analyzed the extension and determined that the majority of infected people were using the Microsoft Edge browser. What's interesting is that the aforementioned hazardous plugin is still available in the Microsoft Edge extension store at the time of writing and has received multiple negative reviews.
How NewTab Wonders is distributed
The malicious browser extension interacts with the computer system and browser in the same way that most other malware does. We noticed that this extension is regularly downloaded by mistakenly clicking an ad element on torrenting platforms and cracked download websites, resulting in drive-by downloads and fraudulent download pages.
These are fairly common, and many people fall for them because they only display after a user clicks the download button on a harmful website. One of the most common websites is file hosting platforms, which have so many advertisements that you'll eventually have to skip 10 of them before you can start downloading. Not to mention that you might not be able to find the file you were looking for in the first place.
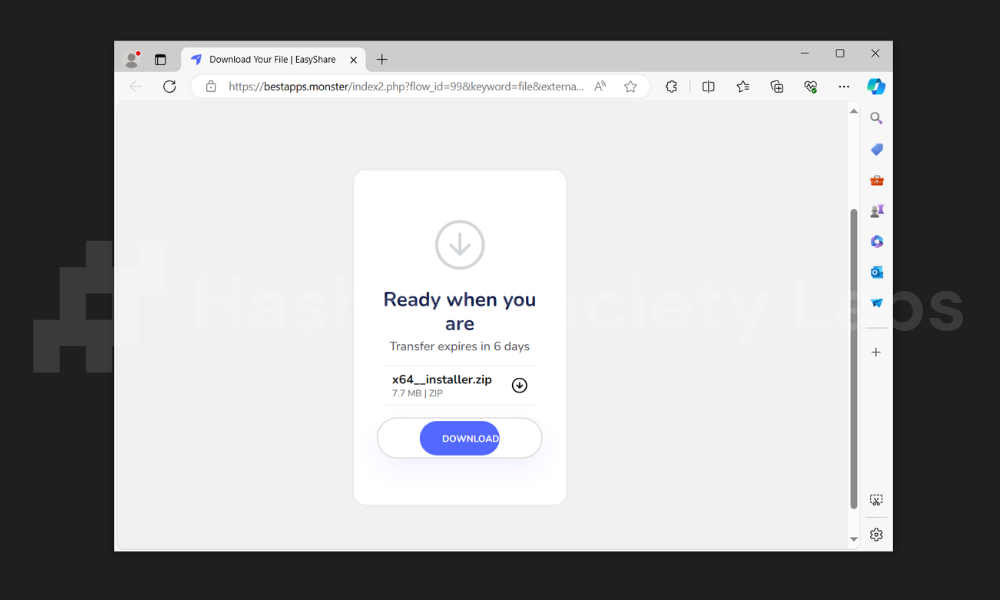
The image above shows a bogus download page from an unsafe torrenting provider that includes NewTab Wonders and other serious malware threats that will be executed when the file is opened. A typical bit of advise to remember when obtaining files from these sites is that you should avoid downloading a movie or game if the file is only a few megabytes in size and if it uses a generic name such as Full_Setup.exe or Setup.exe.
Summary of the threat
| Malware name | NewTab Wonders |
| Extension ID | docmlpbiejclgidiacmjpkpoojgiacgn |
| Redirect URL | Myhoroscopepro.com |
| Threat type | Malicious extension, Browser Hijacker, Adware |
| File type | .json, .zip, .crx |
| Delivery network | Malicious payload via torrent files, cracked software, and drive-by downloads |
| Malware behavior | Change the default search engine to Myhoroscopepro.com |
More about NewTab Wonders
NewTab Wonders is malware that has infected over 3,000 users as of the time of writing. It infects the browser and then vanishes for a while before initiating another malware infection campaign with a different moniker. All while using Myhoroscopepro.com to lead users to either Bing or Yahoo.
If you are unable to delete the NewTab Wonders extension from your browser, please follow the step-by-step tutorial below to remove the harmful extension and any malware payload.
NewTab Wonders removal guide
You've come to the right place if you need help getting rid of the annoying NewTab Wonders browser extension.
This step-by-step guide will show you how to get rid of it from your web browser.
We considered the technical skills of the people who use the internet, so we made sure the steps are simple enough that even those who aren't tech-savvy could follow them.
Before proceeding, make sure you have a backup of your data saved somewhere else.
If you don't, your files may be destroyed or lost as you follow the instructions below. These situations rarely happen, but we recommend doing it just in case.
Remove NewTab Wonders Instantly
Poor protection often leads to malware infection. Let Bitdefender, the world’s leading antivirus, handle NewTab Wonders with ease. It's time to stop worrying about malware.
We've teamed up with Bitdefender to offer Hackerdose visitors an exclusive 50% discount on their products. Now is the time to start taking your computer security seriously with the best antivirus on the planet.
To remove the NewTab Wonders extension from your browser, you only need to follow a simple four-step procedure:
Step 1: Delete the malicious extension
Removing NewTab Wonders may be difficult if certain browser policies are set to make it persist even if you are trying to delete it. It might disable the delete button which makes it hard to do so.
For this reason, we will first need to delete the policies it has set on the browser before attempting to remove the said extension.
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
How to remove Google Chrome browser policies:
1. To do this, we will use Chrome Policy Remover. Download the Windows version by clicking here.

2. Proceed to download delete_chrome_policies.bat by clicking Download anyway.

3. Once the bat file has finished downloading, run it as administrator to begin removing unwanted policies set by the malware.

4. If the Microsoft Defender SmartScreen prevented it from running, click Run anyway. This tool has been recommended enough times in the Google Chrome community therefore we can vouch that it is safe to run. (VirusTotal results of the Policy Remover.)

5. The command prompt will open up, it will close Chrome and delete certain malicious policies. Once the policies are removed, you can now close the command prompt and begin removing the extension.

1. Open the Windows start menu and type Registry Editor.
2. Right-click the first result and select Run as Administrator.
3. In the Registry Editor, go to the following keys and delete each folder one by one:
HKEY_CURRENT_USER\Software\Google\ChromeHKEY_CURRENT_USER\Software\Policies\Google\Chrome
HKEY_LOCAL_MACHINE\Software\Google\Chrome
HKEY_LOCAL_MACHINE\Software\Policies\Google\Chrome
HKEY_LOCAL_MACHINE\Software\Policies\Google\Update
HKEY_LOCAL_MACHINE\Software\WOW6432Node\Google\Enrollment
4. We are not done yet, head over to the following registry key:
HKEY_LOCAL_MACHINE\Software\WOW6432Node\Google\Update\ClientState{430FD4D0-B729-4F61-AA34-91526481799D}
5. Find and delete the value named CloudManagementEnrollmentToken.
6. Lastly, open the File Explorer program and paste the following to the address bar:
%ProgramFiles(x86)%\Google\Policies
7. Select and delete the Policies folder if there is one present.
Following that, close and reopen Google Chrome and the enterprise policy should have been removed.
How to delete unwanted extensions from Chrome:
1. Open Google Chrome and click the three horizontal dots on the upper-right corner of the screen.

2. From the dropdown menu, select Extensions and click Manage Extensions.

3. You should now be able to click the Remove button. Continue to do so in order to remove the unwanted extension from the browser. (For this example, we will be using Google Docs Offline.)

How to remove Mozilla Firefox browser policies:
1. Open the browser and type about:policies in the address bar.

2. Take note of the active policy names as shown on the screen.

3. Press Windows Key + R to open the Run command.

4. Type regedit and hit enter to open the Registry Editor.

5. Go to the following directory: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Mozilla\Firefox

6. Delete the policies that matched the ones shown on the browser policy page earlier. With this, we can proceed with deleting the unwanted extension.

How to remove unwanted extensions from Firefox:
1. Open the Firefox browser and click the extension icon on the upper-right corner of the screen.

2. Click on the cog icon near the unwanted extension you want to install. From the dropdown menu, select Remove Extension. (We will be using a sample extension to demonstrate.)

How to delete browser policies set in Microsoft Edge:
1. Open Command Prompt as administrator.

2. Type in the following code and enter each line separately.
taskkill /im msedge.exe /f
reg delete "HKCU\Software\Policies\Microsoft\Edge" /f
reg delete "HKLM\Software\Policies\Microsoft\Edge" /f3. Once finished, close Command Prompt and we can begin removing the unwanted extension/s from the browser.

How to remove unwanted extensions from Microsoft Edge:
1. Open Microsoft Edge and click the Extensions icon on the top bar of the browser.

2. Click on Manage Extensions.

3. Find the unwanted extension and click Remove.

Step 2: Remove browser malware with AdwCleaner
AdwCleaner is a utility tool that is primarily used for cleaning adware and potentially unwanted applications (PUP) from the computer.
This program is also primarily used to find and remove malware that is targeted at the web browser.
Here's how to install and use AdwCleaner:
1. To start, download the latest version of AdwCleaner.

2. Once AdwCleaner has finished downloading (adwcleaner.exe), run the executable file.

3. If the User Account Control window pops up, click Yes to proceed with running the program.

4. Once the program has launched, agree to the End User License Agreement by clicking the I Agree button.

5. Click on the Scan Now button to begin scanning your computer for browser threats such as adware, PUPs, and more.

6. Wait for AdwCleaner to finish scanning the files on the system. This may take a while depending on how large the files on your device are, as well as your system's hardware capabilities.

7. Once the scan is complete, proceed to take action by following the on-screen instructions. Otherwise, if the scan shows a clean result, click Run Basic Repair to reset Winsock and other settings before finishing the process.

Step 3: Uninstall unwanted software
Unwanted browser extensions may be installed on the computer as a result of malicious software.
Sometimes, this kind of malware can start installing itself on the directory of browser extensions, therefore you should look through the computer for unfamiliar programs that you are not aware of.
While the latest version of Windows allows you to accomplish this through the Add & Remove Programs section, it is still far simpler to use the Programs and Features page in the Control Panel.
The publisher name, the installation date, and the version number will all be displayed in a single grid screen, making it simpler to locate the malware. Here's how to do so:
1. Click on the Windows key to open the Start menu.

2. Type Control Panel in the provided search bar and select the first item from the search results.

3. Click on Programs and inside, select Programs and Features.

4. You will be presented with a list of programs currently installed on your computer.

5. Find programs you do not recognize and right-click the item then select Uninstall/Change from the dropdown menu.

We'll need to use a powerful uninstaller to do the dirty work for us if the software is stubborn and won't go away with normal approaches.
Fortunately, there are tools for this; Revo Uninstaller is a good uninstaller program made to tackle and remove uninstallable programs.
1. To start, download Revo Uninstaller by clicking here. Avoid downloading from third-party sources as they may contain additional bloatware upon installation.

2. On the download page, opt for the free version of Revo Uninstaller as it has all the features we need. Click on Free Download to begin downloading the setup file.

3. The revosetup.exe file would have started downloading. Click on it to start installing the software.

4. Revo Uninstaller setup would now begin and follow the typical setup procedure such as selecting your setup language, accepting the license agreement, and selecting the installation location. Once setup is ready click Install.

5. After the setup is finished, check the Launch Revo Uninstaller option to open the program upon closing the installer.

6. Once Revo Uninstaller has opened, it will show you the list of applications currently installed on the computer. Find the program/s you do not recognize, right-click it, and select Uninstall from the drop-down menu. (We will be using PC App Store to demonstrate.)

7. A confirmation message stating if you are sure you want to uninstall the said program, click Continue.

8. Follow the uninstallation instructions and this time, Revo Uninstaller would have forced the program to continue with the uninstallation compared to the previous attempt via Control Panel.

9. You will be notified that the software has been uninstalled, Revo Uninstaller will now conduct a preliminary examination and get rid of additional files and registries related to the program.

10. On the selection of Scanning modes, select Advanced to make sure everything is scanned without leaving a single directory unnoticed.

11. Wait for the scan to finish as Revo Uninstaller is checking for residual files and registries related to the program.

12. Revo Uninstaller may have found leftover Registry items, click Select All and proceed to delete them by clicking the Delete button next to it. After that, click Next.

13. It may have also found some leftover files and folders, simply do the same by clicking Select All and deleting them. Now click Finish and the uninstallation of the unwanted program is done.

Step 4: Run additional malware scans
Antivirus engines may not detect new threats in the early stages of infection. It might be discovered sooner or later, but it could be too late for the infected computers.
However, new malware threats may contain some strings and signatures from previous malware in a database of other security software. As a result, other antivirus programs may identify it while others do not.
Since some antivirus software may have difficulty detecting the malware, we'll need more than one piece of protection software to help us detect and remove the dangerous threat.
Please run the software individually. You can do so in any particular order.
- Removal Tool
- Emergency Kit
- ESET Scanner
- Malwarebytes
Kaspersky Virus Removal Tool is an excellent tool for scanning and disinfecting malware-infected computers. Please note that this tool is separate from the mainstream Kaspersky security applications, so worry not about the company's controversies.
1. To start, download the Kaspersky Virus Removal Tool.

2. Once the download of the executable file (KVRT.exe) is complete. The program doesn't need to be installed on the computer, so you may begin running it straight away.

3. After reading the KSN Statement, Privacy Policy, and End User License Agreement, check the box indicating your agreement to the terms and conditions. To continue, click Accept.

4. Please wait for the system initialization process to finish, as the program will first check if your system is compatible.

5. Before we start scanning, we will have to set the scope of the scan. Click the Change parameters option to do so.

6. Check all the boxes to allow the computer to search through all of the disks and directories for malware. After that, click OK to return to the main screen.

7. We can now begin the scan; simply click the Start scan button, and the Virus Removal Tool will begin.

8. Await the scan's completion with patience. If there are any risks within the computer system, a notification will be displayed.

9. To completely remove the risks that the program has identified, click Delete from the drop-down menu of each discovered object.

10. Click Continue to remove the identified malware threats from your computer.

As the name implies, the Emergency Kit software by Emsisoft is a must-use in your malware scanner arsenal. It features the same powerful scanning technology used by their flagship software, Emsisoft Anti-Malware.
1. Download the Emsisoft Emergency Kit portable software.

2. You can launch the executable program (EmsisoftEmergencyKit.exe) directly from your downloads folder after downloading it.

3. Click Yes to let the program start on the computer when the User Account Control window appears.

4. Choose your program's destination folder and accept the license and maintenance terms. Next, click Install to continue.

5. Click Malware Scan on the homepage of the Emergency Kit application to start the scanning process. The amount of time it takes for the program to scan your computer will depend on how many files you have and the hardware capabilities of your system.

6. Emsisoft Emergency Scanner will display a list of the files that the program has detected when the scan is complete. To get rid of threats from your computer, click on Quarantine selected.

7. To complete the malware removal procedure, Emsisoft Emergency Scanner may also ask you to restart your computer. Simply click Reboot your system to finish the process.

ESET Online Scanner is a program that is designed only to remove malware threats from your computer for free. It is simple to use and features an advanced malware detection system. There is no need for registration, free trials, or anything else. Simply download, execute, and remove the malware.
1. Download the most recent version of ESET Online Scanner.

2. After pressing the download button, the file (Esetonlinescanner.exe) should have been downloaded to your computer. It does not require any installations so you can simply run the aforementioned file.

3. Before using ESET Online Scanner, it must be initialized. Choose your preferred language and click Get started. Continue as directed by the screen until the homepage appears.

4. Click Computer scan from the homepage, then select Full scan from the three options available.

5. Give ESET Online Scanner the permission to detect and remove potentially unwanted apps by ticking the Enable option. After that, click Start scan to begin the scanning process.

6. Await the completion of the malware scan for your machine by the ESET Online Scanner. ESET Online Scanner would have automatically removed the threats it found after the scan. To complete the malware cleanup process, click Proceed.

Malwarebytes Anti-malware is well-known in the security field; they have helped many people with malware issues through their software, and downloading it will help you as well.
Note: We will only use the free version of Malwarebytes because it includes all of the capabilities we require.
1. Download the latest version of Malwarebytes Anti-malware.

2. Malwarebytes will start downloading (MBSetup.exe) the installation file. Run the executable after the download is complete.

3. To allow the program to execute, simply click Yes in the User Account Control window that may appear.

4. The Malwarebytes setup wizard will now open; select Install to continue.

5. You will be prompted by Malwarebytes to install the Browser Guard extension. Depending on whether you want it on your browser or not, you can choose to download it (the extension is completely free).

6. Please wait as the Malwarebytes Setup installs itself. Follow the on-screen instructions until you have successfully installed Malwarebytes.

7. Start by launching Malwarebytes Anti-malware for the first time after it has been installed. If you're installing Malwarebytes for the first time, you'll get a 14-day free trial of the premium version.

8. After the program takes you to the main dashboard, click the Scanner box in the middle to start scanning the computer.

9. You won't click Scan just yet when you get to the Scanner page. Rather, select Advanced scans as shown below.

10. In the Custom scan section, click Configure scan. We will be able to alter the way the software scans the computer as a result.

11. To detect hidden malware, click the box next to Scan for rootkits on the Configure Custom Scan screen. Additionally, to enable Malwarebytes to scan every drive on your computer, check the boxes next to each one.

12. Once the Custom Scan options have been adjusted, click the Start Custom Scan button to get started.

13. A side window displaying the computer scan's progress will appear. Please wait until Malwarebytes has completed its malware scan of the entire system.

14. Following the completion of the scan, a list of threats found will appear. Check the boxes near all the malicious files and get rid of them from the computer by clicking the Quarantine button.

If prompted, please restart your computer since Malwarebytes may require it.
Since the programs mentioned above are all portable, you can always run them straight from your downloads folder whenever you feel the presence of malware in your computer. We recommend that you organize them all into a single folder for future use.
Optional: Reset the browser
When it comes to browser-targeted malware, it will alter the browser settings for the threat to persist. Therefore simply changing the search engine back to default may not work in many cases.
If the malware still persists, we should reset the web browser to its default settings from when it was first installed. This will get rid of all the configurations the malicious threat has set.
Note: Resetting the browser will get rid of all the data except for saved bookmarks and passwords.
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
1. Open the Chrome browser and click the three horizontal dots at the upper-right corner of the screen.

2. On the dropdown menu, scroll down to the bottom and click Settings.

3. In the left sidebar, scroll down and find Reset settings.

4. Click on Reset settings to their original defaults.

5. A confirmation window will appear, click Reset settings to proceed.

1. Launch the Firefox browser and click the hamburger menu on the upper-right corner of the screen.

2. From the dropdown menu, scroll down and click on Help.

3. Inside the Firefox help menu, click More troubleshooting information.

4. Under Give Firefox a tune up, select Refresh Firefox… to reset the browser.

5. A confirmation window will appear, proceed by clicking Refresh Firefox.

1. Run Microsoft Edge and click on the three horizontal dots on the upper-right side of the screen.

2. From the dropdown menu, select Settings.

3. Open the hamburger menu, scroll down, and select Reset settings.

4. Inside Reset settings, click on Restore settings to their default values.

5. A confirmation window will appear, click Reset to proceed.

After the web browser has finished resetting, download the important extensions you previously used, and pin the tabs you once had. Set it the way it was previously configured before the malware infection.
Malware protection tips
As the saying goes: “The biggest vulnerability is the person behind the screen“
So, here are some tips and what you need to know in order to keep your device safe and malware-free in the long run.
Keep every software installed up to date
Make sure that all of the programs in your computer is up-to-date with the latest version released by the developer. The reason behind this is that these updates frequently tackle bugs and issues that malware actors often exploit.
The same goes for your computer's operating system, make sure Windows is up-to-date with the latest software update to prevent malware from exploiting a hidden vulnerability.
Avoid downloading files from unknown sources
One of the biggest sources of malware infection in a computer system is third-party installations. This happens when a user downloads a certain program from sources that are not the official download links. Some of the common types of sources where malware is present are torrent files, cracked software, and games.
Be careful with opening email attachments
Malware often disguises itself as resumes and quotations and threat actors often send thousands of these infected emails to company employees around the world in order to infiltrate their network.
Always check where your emails are coming from as there may be a chance that the project attachment you received via email did not actually come from a co-worker.
Do not visit unreputable websites
Avoid visiting websites that contain unfiltered advertisements such as illegal streaming websites, cracked software platforms, and links sent out to you by somebody you do not trust.
These sites are often linked to redirect chains that load once you click on an ad element on the page. Following this chain often leads to drive-by malware and phishing pages that an average user may eventually fail to notice.

